Founded in 2009, ZenGRC offers robust, intuitive products that help organizations graduate from manual processes and point solutions, turning compliance and risk management into a source of business advantage. We help organizations better navigate the complexities of governance, risk, and compliance.
Your compliance team runs two programs that should be one. HIPAA lives with legal and privacy. HITRUST lives with infosec. Both teams collect overlapping evidence, maintain separate spreadsheets, and scramble before audits—with zero visibility into what the other is doing.
For healthcare technology companies managing multiple frameworks with three to five people, this HITRUST and HIPAA fragmentation is expensive, error-prone, and increasingly risky. In 2025, HHS enforcement accelerated dramatically, with 19 or more settlements announced through August alone. The proposed HIPAA Security Rule update would cost the industry an estimated $9 billion in year one and eliminate the distinction between “required” and “addressable” safeguards entirely.
Let’s dive into managing HITRUST and HIPAA simultaneously:
- The Two Worlds Problem
- Where HITRUST and HIPAA Overlap (and Where They Don’t)
- The Compliance Treadmill
- The Real Cost of Manual Management
- What Purpose-Built GRC Means for Healthcare Tech
- Moving to Continuous Assurance
The Two Worlds Problem
HIPAA requires organizations to designate both a Privacy Officer and a Security Officer. In healthcare tech companies, these roles sit in different departments with different tools, timelines, and vocabularies.
Legal and privacy teams manage Business Associate Agreements, breach notification, and patient access rights. Security teams manage technical safeguards, access controls, encryption, and vulnerability scanning. Both conduct risk assessments. Both track vendors. Both collect evidence mapping to many of the same requirements.
For healthcare tech companies with 1,000 to 5,000 employees, this fragmentation is especially painful. You have enough complexity to require formal programs for HIPAA, HITRUST, and SOC 2, but not the 20-person compliance departments to absorb the overhead of parallel workflows. The result: duplicated work, inconsistent documentation, and gaps that only surface during external assessments—exactly when they cost the most to fix.
Where HITRUST and HIPAA Overlap (and Where They Don’t)
HITRUST CSF harmonizes more than 60 authoritative sources—including HIPAA, NIST 800-53, SOC 2, ISO 27001, and PCI DSS—into a single control set. A HITRUST r2 assessment covers approximately 360 requirement statements and addresses all HIPAA Security Rule requirements.
The overlap is significant. Access control policies, risk assessments, incident response documentation, encryption configurations, audit logs, training records, and vendor management evidence all map across HIPAA, HITRUST, and SOC 2 simultaneously.
As Aaron Zollman, CISO at Cedar, explained to CSO Online: “When auditors ask ‘show me your compliance with HIPAA Security Rule part 164.308,’ I open my HITRUST book to section 00.a and pull the evidence I’ve already pulled. You don’t have to redo the work.”
But the overlap isn’t identical. HIPAA’s Privacy Rule imposes obligations around data use, disclosure, and patient rights that HITRUST addresses but doesn’t fully replicate. HITRUST CSF demands maturity scoring across policy, procedure, and implementation levels—documentation depth HIPAA doesn’t explicitly require. SOC 2 adds criteria around availability and processing integrity that extend beyond both frameworks.
The practical challenge isn’t whether frameworks overlap—it’s whether your team can identify, track, and reuse evidence across all three without manual reconciliation. For a HITRUST r2 assessment with 360 requirements scored across three maturity levels, that’s roughly 900 evidence references. Add HIPAA documentation (retained for six years) and SOC 2 audit evidence, and you’re managing thousands of artifacts needing consistent formatting, current dates, and clear chains of custody.
When two separate teams manage these artifacts in separate systems, evidence reuse becomes theoretical rather than practical.
The Compliance Treadmill

Healthcare tech companies face overlapping cycles that keep compliance teams in perpetual assessment mode:
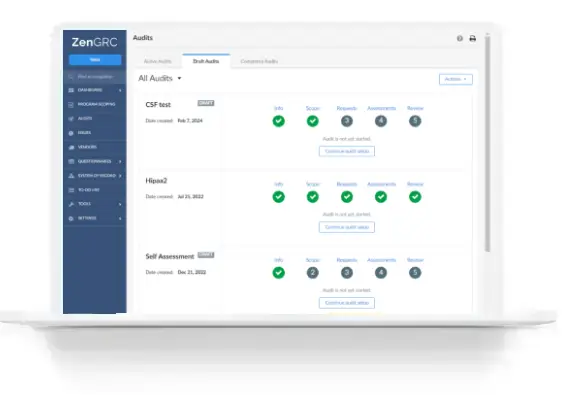
- HITRUST r2 lasts two years but requires a mandatory interim assessment at one year. First-time certification takes 9-18 months.
- HITRUST i1 lasts one year, with strict thresholds for rapid recertification.
- SOC 2 audits typically run annually with multi-month observation periods.
- HIPAA compliance is continuous, requiring annual risk analyses, workforce training, and vendor reviews. The proposed Security Rule update would add mandatory annual penetration testing and semi-annual vulnerability scanning.
Without a unified system tracking timelines and connecting evidence to requirements, teams default to reactive firefighting instead of maintaining continuous compliance.
The Real Cost of Manual Management
For healthcare specifically, the stakes are higher. Healthcare has been one of the most expensive industry for data breaches: OCR’s Risk Analysis Initiative drove the majority of recent actions, with risk analysis failures appearing in 13 of 20 cases. Penalties ranged from $10,000 to $3 million. Solara Medical Supplies paid $3 million to OCR plus an additional $5 million to settle a class action lawsuit.
The Ponemon Institute calculates that the average cost of non-compliance is $14.8 million—2.71 times higher than the average cost of compliance at $5.5 million.
What Purpose-Built GRC Means for Healthcare Tech
Generic compliance tools don’t fit healthcare tech companies running HIPAA, HITRUST, and SOC 2 with small teams. Purpose-built GRC for this use case means a platform designed around three realities:
Bridging the Organizational Divide

When privacy teams track HIPAA in one system and security teams track HITRUST in another, evidence reuse becomes impossible. A purpose-built platform provides a single environment where both teams work, with field-level permissions giving each access to relevant controls, evidence, and workflows. Legal sees BAA management and privacy controls. Infosec sees technical safeguards and assessment scoring. Leadership sees consolidated dashboards.
Automating Evidence Collection
The highest-value capability for small teams is automated evidence collection with cross-framework mapping. When a single screenshot of an encryption configuration satisfies HIPAA Security Rule 164.312, HITRUST control 01.v, and SOC 2 CC6.1, it should be collected once, mapped automatically, and reused across all three assessments.
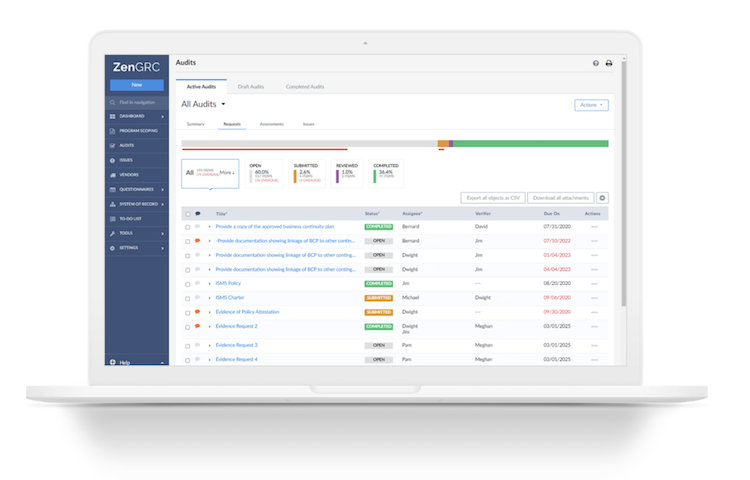
Platforms like ZenGRC connect to 45+ integrations to pull evidence directly from cloud infrastructure, identity providers, and ticketing systems—shifting team time from collecting screenshots to reviewing controls and addressing gaps.
Supporting Chain of Custody
HITRUST assessments require strict evidence chains dated, attributed, and traceable through validation and certification. HIPAA requires six-year documentation retention. Spreadsheets can’t provide this audit trail reliably. Workflow engines that track every approval, review, and change with timestamps create the documentation chain assessors and regulators expect.
Moving to Continuous Assurance
The regulatory environment is intensifying on every front. OCR’s third phase of audits is reviewing 50 entities with a focus on hacking and ransomware. The proposed Security Rule update would mandate encryption, MFA, annual penetration testing, and 72-hour system restoration capabilities. State attorneys general are pursuing cases independently, and the DOJ has confirmed that cybersecurity failures can trigger False Claims Act liability even without actual breaches.
The compliance surface area is growing, not shrinking. For mid-market healthcare tech companies, the question isn’t whether to invest in GRC infrastructure—it’s whether to invest in the right kind.
Purpose-built GRC for this segment requires fast implementation (weeks, not months), cross-framework evidence mapping at the artifact level, workflow capabilities supporting chain of custody documentation, and design philosophy built around three to five person teams managing multiple frameworks simultaneously.
Healthcare tech companies that treat compliance as ongoing operational capability gain measurable advantages. HITRUST reports a 99.41% breach-free rate among certified environments.
Your team of three to five people is capable of managing HIPAA, HITRUST, and SOC 2 together. They just need tools designed for the way healthcare tech compliance actually works.
Ready to see how ZenGRC bridges the HIPAA and HITRUST compliance gap? Request a demo to see cross-framework evidence mapping, automated evidence collection, and workflow-driven chain of custody documentation built for healthcare tech compliance teams.