ZenGRC offers robust, intuitive products that help organizations graduate from manual processes and point solutions, turning compliance into a source of business advantage. We help organizations better navigate the complexities of governance, risk, and compliance.
The core benefits of a GRC tool are unified visibility across all your compliance and risk programs, elimination of duplicate work across frameworks, automated evidence collection, continuous audit readiness, and a single source of truth that holds up to external scrutiny. For mid-market organizations managing multiple frameworks with lean teams, a purpose-built GRC tool is the difference between a compliance program that scales and one that compounds overhead every time a new requirement is added.
Here’s what those benefits actually mean for a three-to-ten person compliance team managing SOC 2, HIPAA, NIST, and ISO 27001 without burning out or burying the CISO in spreadsheet reconciliation every quarter:
What does a GRC tool actually do?
A GRC tool centralizes all compliance evidence and controls in one place, maps those controls across multiple frameworks simultaneously, automates evidence collection from the systems your organization already uses, and tracks every action — who reviewed what, when, what changed, who approved it — so you have a complete audit trail without maintaining one manually.
What it is not is a checklist. The value isn’t that a GRC tool tells you what to do. It’s that it builds the infrastructure that makes doing it — and proving you did it — dramatically less expensive in time, labor, and risk. Before getting into the specific benefits, that distinction matters: a purpose-built GRC tool doesn’t just organize your compliance program. It changes the economics of running one.
Does a GRC tool eliminate duplicate compliance work?
Yes — and for most mid-market compliance teams, this is the one of the top benefits of a GRC tool.
When compliance programs live in spreadsheets, every framework is its own island. SOC 2 evidence lives in one file. HIPAA documentation lives in another. NIST controls are tracked somewhere else. When an auditor requests evidence that spans multiple frameworks — and it almost always does — someone has to manually reconcile systems that were never designed to talk to each other.
The duplication is significant. For compliance teams managing three or more frameworks manually, the same evidence gets collected separately for each — by different people, formatted differently, with no single record linking them. At a certain point, the overhead stops being manageable and starts being a liability.
A GRC tool eliminates this through cross-framework control mapping. When a single encryption configuration satisfies HIPAA Security Rule §164.312, SOC 2 CC6.1, and ISO 27001 Annex A.8.24, it is collected once and automatically mapped to all three. When a risk assessment is completed for ISO 27001, the documentation satisfies the HIPAA annual risk analysis requirement at the same time. The work happens once. The credit applies everywhere it’s earned.
For a compliance team of five people managing three frameworks, this isn’t a marginal efficiency gain. It’s the difference between keeping pace with your compliance obligations and falling behind them.
How does a GRC tool improve audit evidence?
A GRC tool improves audit evidence by replacing manually assembled, inconsistently formatted documentation with a structured, automatically logged evidence repository — one where every artifact is timestamped, attributed, and traceable from requirement to control to proof.

Auditors aren’t looking for good intentions. They’re looking for documentation that tells a coherent, traceable story: this control was designed this way, implemented by this person, reviewed on this date, approved by this individual, and tested against this requirement. When that story is spread across multiple spreadsheets with no version control and no chain of custody, auditors see gaps — even when the underlying controls are sound.
For compliance teams managing multiple frameworks across disconnected tools, this is where programs that are functionally compliant still produce audit findings. The controls exist. The evidence doesn’t hold together.
A purpose-built GRC platform changes what auditors see. Every action is logged automatically. Evidence is formatted consistently, retained for required periods — six years for HIPAA documentation, for example — and traceable without manual reconstruction. The practical result is that audits become conversations about your program rather than investigations into your documentation. Improving audit evidence is another one of the benefits of a GRC tool.
Does a GRC tool improve audit readiness?
Yes — and more importantly, it changes what audit readiness means. With spreadsheet-based compliance, audit readiness is a sprint: an intense period of evidence gathering, reconciliation, and gap patching that happens two to three times a year. With a GRC tool, audit readiness is a continuous posture.
Organizations that rely on spreadsheets operate reactively. Controls degrade between audit cycles. Issues that would be easy to address in January become expensive findings in October, when there’s no time to remediate before the auditor arrives. Automated monitoring in a GRC platform eliminates this pattern by tracking control effectiveness in real time. When a control fails — a system configuration drifts, an access review goes overdue, a vendor assessment expires — the right person is notified immediately. The issue is addressed when it’s small, not when it’s a finding.
This posture has measurable business value. HITRUST reports a 99.41% breach-free rate among certified environments — organizations that have invested in exactly this kind of continuous compliance infrastructure. The Ponemon Institute calculates that the average cost of non-compliance is $14.8 million — 2.71 times higher than the average cost of compliance at $5.5 million. Continuous audit readiness isn’t a premium. It’s the cheaper option.
Audit readiness is one of the most concrete benefits a GRC tool delivers – but the full picture goes deeper than a faster evidence pull. The sprint model fails compliance teams not because of effort, but because manual processes have no mechanism for continuous monitoring. Controls drift. Issues that are small in January become findings in October. For teams running three or more frameworks with no audit calendar overlap, the sprint never fully ends. It just changes names. A purpose-built GRC tool changes what audit readiness means: not a state you manufacture before each cycle, but one your program maintains year-round. For a closer look at what that shift looks like in practice – and why it matters for lean teams managing multiple frameworks – read: The Benefits of Audit Readiness Becoming a Posture, Not a Sprint.
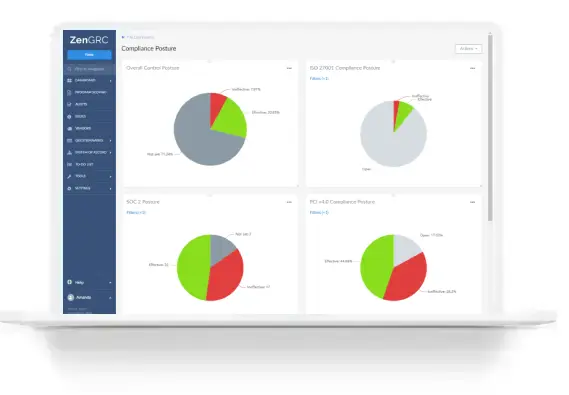
How does a GRC tool give leadership better visibility?

A GRC tool gives leadership real-time visibility into compliance posture across all active frameworks simultaneously — replacing the quarterly manual report with a live dashboard that reflects the current state of the program at any point, without anyone having to compile it.
A CISO managing three frameworks across three spreadsheets owned by three different people cannot answer confidently: “Where are we across all frameworks right now?” Getting a real answer requires manual aggregation that is itself a compliance risk — because the reconciliation may not happen before an audit surfaces a gap.
Real-time dashboards change how the board and executive team engage with compliance. Risk scores, control status, remediation timelines, outstanding evidence requests, and upcoming audit milestones are all visible in one place. When leadership can see the current state of the program continuously — not just when someone has time to prepare a report — GRC stops being a periodic check-in and starts being a continuous input into business decisions. New contracts, new markets, new acquisitions all carry compliance implications. An executive team with real visibility can evaluate those implications in real time, not retroactively.
Can a small compliance team manage multiple frameworks with a GRC tool?
Yes — and for most mid-market organizations, a purpose-built GRC tool is the only way a small team can realistically manage multiple frameworks without falling behind or burning out.
Mid-market organizations face a compliance paradox: they operate at enough scale to require formal programs across multiple frameworks, but they don’t have the 20-person compliance departments that enterprise organizations use to absorb the overhead. A healthtech company running HIPAA, HITRUST, and SOC 2 with four compliance professionals is not an edge case. It’s a representative customer.
The manual overhead of multi-framework compliance is not proportional to team size — it compounds. A five-person team running three frameworks manually is not three times busier than a team running one. The duplication, the reconciliation, the audit preparation all multiply as frameworks accumulate. Without a system designed to absorb that compounding, the work either falls behind or the team burns out.
Purpose-built GRC tools are designed around this reality. Automated evidence collection handles the administrative burden that consumes most of audit season. Cross-framework mapping eliminates duplication. Workflow engines manage task assignment, reminders, and escalations so nothing falls through the cracks when a team member is on vacation or a key role turns over. A small team using the right tools outperforms a larger team using the wrong ones — not because of heroics, but because the infrastructure does the work that shouldn’t require human judgment.
For more about managing multiple compliance frameworks within one GRC tool, read: Tools for Managing Multiple Compliance Frameworks: What to Look For
Does a GRC tool help with staff turnover?
Yes — significantly. Compliance programs built on spreadsheets are also built on people. When a compliance analyst leaves, the institutional knowledge of which file is current, how controls were mapped, and which evidence collection process actually works leaves with them.

A GRC platform is, among other things, an institutional knowledge system. Every decision is documented, every process is embedded in the platform, and every piece of evidence is traceable regardless of who collected it. When a new compliance manager joins, they inherit a functioning program with a complete history — not a folder of spreadsheets they didn’t build and can’t fully interpret.
For organizations managing complex, multi-year compliance programs across frameworks with strict chain-of-custody requirements — HITRUST r2, for example, with its mandatory interim assessments — this continuity isn’t a convenience. It’s operationally essential.
How to choose a GRC tool?
Not all GRC tools are built the same way, and the wrong platform can create as much overhead as it removes. The criteria that matter most for mid-market compliance teams are:
Cross-framework mapping at the control level. The platform should map individual controls to specific requirements across every framework in scope — not just identify which frameworks overlap, but tell you exactly which control satisfies which requirement in which framework, with the evidence to prove it.
Automated evidence collection through native integrations. Manual evidence collection defeats the purpose. Look for platforms with direct integrations into your cloud infrastructure, identity providers, ticketing systems, and security tools — so evidence is pulled automatically, not assembled by hand.
Fast implementation. Some GRC platforms take months or years to implement. For mid-market teams, that’s not viable. The right platform should be operational in weeks, not quarters, with minimal business disruption.
Workflow and chain-of-custody documentation. Every review, approval, and change should be logged automatically — required for HITRUST certification, expected in regulated industries, and the foundation of an audit trail that holds up to external scrutiny.
AI trained on your data. The most advanced GRC platforms now use AI to do analyst-level work: scoping new programs, designing controls, assessing evidence, generating audit structure. That AI should be trained on your organization’s data only — not on global training sets that introduce security and privacy risks.
Predictable, all-inclusive pricing. Hidden costs and per-user pricing models that penalize growth are common in enterprise GRC. A platform with straightforward pricing lets you extend access to control owners, auditors, and leadership without license costs multiplying as your program matures.
Knowing you need a GRC tool is one thing. Knowing which one to choose is harder. The criteria that matter, the red flags to watch for, and the questions to bring into vendor conversations are covered in the full evaluation guide. Read: How to Choose a GRC Tool: An Evaluation Guide.
What is the cost of not using a GRC tool?
The cost of not using a GRC tool is not just inefficiency — it’s financial exposure that grows every time your compliance obligations expand and your manual processes fail to keep pace.
The Ponemon Institute research is concrete: organizations that enable compliance technology see an average of $1.02 million in cost savings. The inverse is more compelling: non-compliance costs an average of $14.8 million — not because compliance software is magic, but because organizations without systematic compliance infrastructure find issues late, remediate expensively, and face enforcement actions that well-run programs prevent entirely.
In healthcare, OCR’s enforcement trajectory makes the stakes explicit. In 2025, HHS announced 21 settlements. Risk analysis failures appeared in 13 of 20 enforcement cases. Penalties ranged from $10,000 to $3 million per violation. Solara Medical Supplies paid $3 million to OCR plus an additional $5 million in class action settlement — for a breach that a documented, functioning risk analysis process would likely have addressed before it became a reportable incident.
Spreadsheets don’t scale. As compliance obligations expand — new frameworks, new jurisdictions, new vendor requirements — the manual overhead compounds. What works for one framework becomes unmanageable at three. A GRC tool isn’t an expense. It’s the infrastructure that determines whether your compliance program is an operational asset or a recurring crisis.
Now that we know the benefits of a GRC tool, are you ready to see what a purpose-built GRC tool looks like in practice? ZenGRC centralizes compliance evidence, automates collection across 45+ integrations, and maps controls across 30+ frameworks — including SOC 2, HIPAA, NIST, ISO 27001, HITRUST, and PCI DSS — so your team tests once and satisfies many. Book a demo to see how lean compliance teams replace spreadsheet overhead with a program built to scale.